Securing your wallet
Introduction
Wallet security can be broken down into two independent goals:
- Protecting your wallet against loss.
- Protecting your wallet against theft.
In the case that your current wallet hasn't been protected adequately (e.g. put online with a weaker password):
- Making a new secure wallet, using appropriate long-term protection.
For a brief overview see also: Wallet Security Dos and Don'ts
Paper Wallets
Paper wallets are a fairly simple way to store your bitcoins independent of a computer. When generated securely and stored on paper, or other offline storage media, a paper wallet decreases the chances of your bitcoins being stolen by hackers, or computer viruses.
With each entry on a paper wallet, you are securing a sequence of secret numbers that is used to prove your right to spend the bitcoins assigned to one of your addresses. This secret number, called a private key, is most commonly written as a sequence of fifty-one alphanumeric characters, beginning with a '5'.
One way you can create a paper wallet is by going to the website bitaddress.org. This website features a free client-side paper wallet generator written in JavaScript. The webpage can be saved as a file and used on an offline computer. Using it online is relatively safe, for storing smaller amounts, but not airtight unless you take extra precautions to ensure your keys are not stolen by spyware. Alternatively Blockchain.info offers a tutorial on how to generate a paper wallet with an online component so you can still check your balance easily.
To generate a safer paper wallet, it is best to "clean-boot" your computer with a bootable CD (such as a Linux Live CD), with your computer not connected to the Internet, to ensure that you do not have any active spyware that might steal any private keys you generate. Disconnecting from the Internet allows you to confirm that the paper wallet generator is truly self-contained and isn't depending on communication with a remote server. Run the saved paper wallet generator in a web browser, then print your paper wallets or store them on external media (do not save them on the computer), and then shut down the computer. You may need to load an appropriate printer driver in order to print while booted from the live CD.
A paper wallet lists multiple Bitcoin addresses and their corresponding private keys. You can send Bitcoins to any address on the page and they will be inaccessible until the private key is imported into a wallet. Since version 0.6.0, the bitcoin software has a command called "importprivkey" that can load private keys, but you can also use the "Add Funds" - "Private key" screen at MtGox or Blockchain.info's "My Wallet" service to recover bitcoins from a private key. In the case of MtGox, bitcoins are deposited in your account, and can be sent out of MtGox after the standard number of deposit confirmations.
Remember, spyware and viruses often attempt to monitor your computer activities so that their authors can steal from you. They are interested in passwords to online accounts, and anything of value. Bitcoin wallets and private keys are something of value that have already been targeted by malware. Paper wallets isolate you from much of this risk.
If your computer is infected with spyware or viruses - even if there are no symptoms, or your antivirus isn't reporting anything - then anything you type, view, or save on your computer, could potentially be stolen by someone remotely controlling your computer. Your private key can then be intercepted while you enter it, so only enter a Bitcoin private key into your computer when your intent is to redeem its value immediately.
Hardware wallets
They are not operational yet, but Hardware wallets are a major effort to provide a good combination of enhanced security and usability.
Importance of security updates
No software is perfect, and from time to time there may be security vulnerabilities found in your Bitcoin client as well. Be sure you keep your client updated with the latest bug fixes, especially when a new vulnerability is discovered. We maintain a list a known vulnerabilities on this wiki - you can watch that page to get updates. Note that you don't need to be running the latest major client version: some clients, including the popular Bitcoin-Qt, have older versions available with bugfix-only updates.
Securing the Bitcoin-QT or bitcoind wallet
Bitcoin transactions send Bitcoins to a specific public key. A Bitcoin address is an encoded hash of a public key. In order to use received Bitcoins, you need to have the private key matching the public key you received with. This is sort of like a super long password associated with an account (the account is the public key). Your Bitcoin wallet contains all of the private keys necessary for spending your received transactions. If you delete your wallet without a backup, then you no longer have the authorization information necessary to claim your coins, and the coins associated with those keys are lost forever.
The wallet contains a pool of queued keys. By default there are 100 keys in the key pool. The size of the pool is configurable using the "-keypool" command line argument. When you need an address for whatever reason (send, “new address”, generation, etc.), the key is not actually generated freshly, but taken from this pool. A brand new address is generated to fill the pool back to 100. So when a backup is first created, it has all of your old keys plus 100 unused keys. After sending a transaction, it has 99 unused keys. After a total of 100 new-key actions, you will start using keys that are not in your backup. Since the backup does not have the private keys necessary for authorizing spends of these coins, restoring from the old backup will cause you to lose Bitcoins.
Creating a new address generates a new pair of public and private keys, which are added to your wallet. Each keypair is mostly random numbers, so they cannot be known prior to generation. If you backup your wallet and then create more than 100 new addresses, the keypair associated with the newest addresses will not be in the old wallet because the new keypairs are only known after creating them. Any coins received at these addresses will be lost if you restore from the backup.
The situation is made somewhat more confusing because the receiving addresses shown in the UI are not the only keys in your wallet. Each Bitcoin generation is given a new public key, and, more importantly, each sent transaction also sends some number of Bitcoins back to yourself at a new key. When sending Bitcoins to anyone, you generate a new keypair for yourself and simultaneously send Bitcoins to your new public key and the actual recipient's public key. This is an anonymity feature – it makes tracking Bitcoin transactions much more difficult.
So if you create a backup, do more than 100 things that cause a new key to be used, and then restore from the backup, some Bitcoins will be lost. Bitcoin has not deleted any keys (keys are never deleted) – it has created a new key that is not in your old backup and then sent Bitcoins to it.
Making a new wallet
If a wallet or an encrypted wallet's password has been compromised, it is wise to create a new wallet and transfer the full balance of bitcoins to addresses contained only in the newly created wallet. Examples of ways a wallet may be compromised are through password re-use, minimal strength passwords, computer hack or virus attack.
There are a number of ways to create a new wallet with Bitcoin-QT or bitcoind but this is a process that has been tested with bitcoind 0.6.3. We use the copy command to minimize the chance of any data loss but you are warned to make backups of any wallet.dat that holds a balance for you.
- 1. Shut down the Bitcoin program.
- 2. Find and make a backup of the "compromised" wallet.dat file and rename it, perhaps adding a short description:
- wallet.dat -> wallet-compromised.dat
- Depending on your OS, the wallet file will be located at:
- Windows: %APPDATA%\Bitcoin\
- Linux: ~/.bitcoin/
- Mac: ~/Library/Application Support/Bitcoin/
- 3. Start the Bitcoin program and it will create a new wallet.dat. You may then encrypt the wallet as desired and make a new backup.
- 4. Once you've made a new wallet, you can obtain one or more addresses and copy them into a text editor. After obtaining the new address(es), shut down the Bitcoin program, make a backup of the new wallet.dat file and copy it to a new file named wallet-new.dat.
- 5. Copy the wallet-compromised.dat file back to wallet.dat, start the Bitcoin program and transfer your balance to the new address(es) you put in your text editor. Once the balance is back to 0 for your compromised wallet, you may want to wait a couple minutes or for a confirmation or check block explorer to be sure the transactions have been broadcasted. Then you may shut down the Bitcoin program.
- 6. Rename wallet.dat to wallet-compromised.dat.
- 7. Rename wallet-new.dat to wallet.dat.
You should now have a new wallet with all the bitcoins from the old wallet.
Making a secure workspace
If you are using your computer to handle bitcoins, a wallet, Bitcoin-related passwords, or Bitcoin private keys, you must take care that the system is free of malware, viruses, keyloggers, remote access tools, and other tools that may be used to make remote copies of any of the above. In the case that your computer is compromised, the precautions taken below may provide additional protection.
Debian-based Linux
The first step is to make a new user. In order for that new user to have an encrypted home directory, you'll first need the encryption utility. Run:
sudo apt-get install ecryptfs-utils
Now you're ready to create a new user
sudo adduser --encrypt-home new_user_name
You'll need to come up with a secure new password for that user.
When you get to the prompt 'Enter the new value, or press ENTER for the default', just keep hitting ENTER.
Then switch user to the new user. To get to the new user you can use the switch user icon for your system, which on Ubuntu is in the 'System/Quit' screen, or if there is no switch icon on your system you can log out and log back in as the new user.
Since the home folder of this user is encrypted, if you're not logged in as that user, data that is saved there can't be browsed, even by a root user. If something goes wrong with your system, and you need to decrypt the new user's files, you'll need its decryption key.
ecryptfs-unwrap-passphrase
It will ask you for your user's password and give you the decryption key. WRITE DOWN OR SAVE THE CODE IT RETURNS because you will need it if you ever have to pull your data off while the OS is not working. (You can run it again later if you need to, but run it now so that you can get your data if your Linux install gets botched.)
The encrypted folder data is not encrypted while it's in memory, and so if it's ever sent to the swap partition it can be stolen from there unless that too is encrypted - be aware that this will mean you cannot use Hibernate anymore, as the bootloader won't be able to restore the hibernation data.
ecryptfs-setup-swap
Then click on a folder in the new user to display the file browser, then keep going up folders until you see the new user home directory, then right click to bring up the Properties dialog, then click on the Permissions tab, then in the Others section, set the folder access to None.
For secure browsing, open Firefox, and then go into the Edit menu and click Preferences. Starting from the left, click on the General tab, and in the 'Startup/When Firefox starts' pop up menu, choose 'Show a Blank Page'. Then click on the Content tab, and deselect 'Load images automatically' and deselect 'Enable JavaScript'. Then click on the Privacy tab, and in the 'History/Firefox will' pop up menu, choose 'Never remember history'. Then click on the Security tab, and in the Passwords section, deselect 'Remember passwords for sites' and deselect 'Use a master password'. Then click on the Advanced tab, then click on the Update tab, and then in the 'Automatically check for updates to' section, deselect 'Add-ons' and 'Search Engines'.
When JavaScript is disabled, the Linux download page will not download automatically, so you'll have to click on the 'direct link' part of the "Problems with the download? Please use this 'direct link' or try another mirror." line.
Mac
This solution does not scale; the amount of needed space can grow beyond the image size.
Backup all data
Follow these instructions to backup all the bitcoin data (wallet and block chains) to an encrypted disk image.
- Open Disk Utility
- Click New Image and choose a big enough size, 128-bit or 256-bit (faster or more secure) encryption and single partition.
- Save it somewhere you won't lose it (like your Wuala, Dropbox, Strongspace or whatever)
- Choose a safe and strong password
- Move everything from ~/Library/Application Support/Bitcoin/ to the image
- Symlink it back so the app would be able to use it
- ln -s /Volumes/Bitcoin ~/Library/Application Support/Bitcoin
Don't forget to mount your image before using Bitcoin and unmount it after quitting.
Backup just wallet.dat
Follow these instructions to backup just the wallet.dat file. This results in a smaller disk image, but it's more complicated to do.
- Open Disk Utility
- Click New Image and choose a big enough size, 128-bit or 256-bit (faster or more secure) encryption and single partition.
- Save it somewhere you won't lose it (like your Wuala, Dropbox, Strongspace or whatever)
- Choose a safe and strong password
- Move your wallet.dat file to the image
- Symlink it back so the app would be able to use it
- ln -s /Volumes/Bitcoin/wallet.dat ~/Library/Application Support/Bitcoin/wallet.dat
Don't forget to mount your image before using Bitcoin and unmount after quitting it.
Note: If you start the Bitcoin application without having the image mounted, the application will overwrite your symlink with a new wallet. If that happens, don't panic. Just delete the new wallet.dat, mount the image, and recreate the symlink like above.
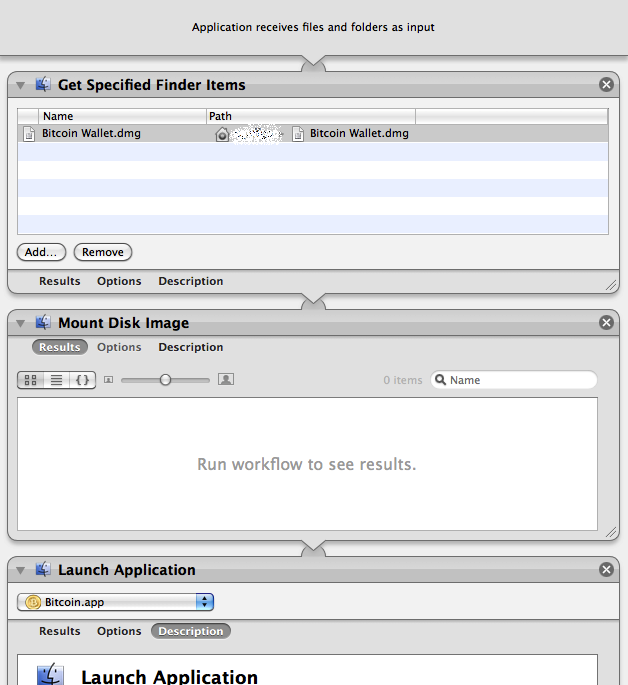
Automation: You can create a small application using Automator (included in OS X) to automatically mount the wallet and then launch Bitcoin App. See the Screenshot on how to do this.
If one doesn't want to use encrypted Disk images, then a small shell script can be used instead that takes care of decrypting the wallet, launching bitcoin client, and encrypting it after the client exits. This script works on both OSX and Linux: bitcoin-launch-script
Windows
Due to the frequency with which Windows computers are compromised, it is advised to encrypt your wallet or to keep your wallet on an encrypted disk image created by third-party software, such as TrueCrypt (open source) or Jetico BestCrypt (commercial). This also applies to the storage of passwords, private keys and other data that can be used to access any of your Bitcoin balances.
Assuming that you have installed the Windows Bitcoin client and run it at least once, the process is described below.
To mount the Bitcoin data directory on an encrypted drive
- Use the third-party disk image encryption program of your choice to create and mount an encrypted disk image of at least 5GB in size. This procedure stores the entire block chain database with the wallet.dat file so the required size of the encrypted disk image required may grow in the future.
- Locate the Bitcoin data directory, and copy the directory with all contents to the encrypted drive.
For help finding this directory, see Locating Bitcoin's Data Directory.
- Create a Windows shortcut that starts Bitcoin with the
-datadirparameter and specifies the encrypted drive and directory.For example, if you installed Bitcoin in the default directory, mounted your Bitcoin encrypted drive as
E:\, and stored your Bitcoin data directory on it asBitcoin, you would type the following command as the shortcut Target:C:\Program Files\Bitcoin\bitcoin.exe -datadir=E:\Bitcoin - Open Bitcoin's settings and configure it NOT to start automatically when you start Windows.
This is to allow you to mount the Bitcoin encrypted disk image before starting Bitcoin.
- Shut down Bitcoin, and then restart it from the new shortcut.
After doing this, any time you want to use Bitcoin, you must first mount the Bitcoin encrypted disk image using the same drive designation, and then run Bitcoin from the shortcut that you created, so that it can find its data and your wallet.
Locating Bitcoin's data directory
The data directory is the location where Bitcoin's data files are stored, including the wallet data file.
Windows
Go to Start -> Run (or press WinKey+R) and run this:
explorer %APPDATA%\Bitcoin
Bitcoin's data folder will open. For most users, this is one of the following locations:
C:\Documents and Settings\YourUserName\Application data\Bitcoin (Windows XP) C:\Users\YourUserName\Appdata\Roaming\Bitcoin (Windows Vista and 7)
If you have trouble browsing to these folders, note that "AppData" and "Application data" are hidden by default.
Linux
By default Bitcoin will put its data here:
~/.bitcoin/
You need to do a "ls -a" to see directories that start with a dot.
If that's not it, you can do a search like this:
find / -name wallet.dat -print 2>/dev/null
To change the directory Bitcoin stores its data in:
Run in terminal or script: ./bitcoin(-qt) -datadir=./[Directory_Name]
Mac
By default Bitcoin will put its data here:
~/Library/Application Support/Bitcoin/
Backup
Note: Using Dropbox to back up your Bitcoin data is not recommended as doing so introduces the following security concerns:
- Dropbox stores your encryption key (meaning that a disgruntled Dropbox employee or an attacker who gained access to the system could decrypt your Dropbox data and steal your bitcoins)
- the Dropbox client only needs a password for the first login. After it authenticates once, the server assigns it a token which it uses to show that, at one time, its user knew the password rather than sending the actual password (meaning that if you ever use the Dropbox client on another PC, that PC's users can access your Dropbox - even if you change your password - and can steal your bitcoins or get a virus that will steal your bitcoins).
For these reasons, an alternative that always uses password authentication such as Wuala should be used. Wuala's servers do not store your encryption key and the program authenticates with the password each time it is started.
Whether you use Dropbox as your backup or not, it is advised to use what Steve Gibson calls "pre-Internet encryption" which means to use some form of encryption on your files before you back them up, in case an attacker gains access to that backup. Make sure to pick a password that is memorable but secure.
The only file you need to back up is "wallet.dat" which can be done one of two ways. To make a copy of the wallet.dat file, ensure that Bitcoin is closed and copy this file somewhere else. The other way is to use the backupwallet JSON-RPC command to back up without shutting down Bitcoin.
Once a copy has been made, encrypt it, and put it in two or more safe locations. Consider the risk due to theft, fire, or natural disaster in proportion to the value of bitcoins stored in the wallet.
General Solutions
Your wallet.dat file is not encrypted by the Bitcoin program by default but the most current release of the Bitcoin client provides a method to encrypt with a passphrase the private keys stored in the wallet. Anyone who can access an unencrypted wallet can easily steal all of your coins. Use one of these encryption programs if there is any chance someone might gain access to your wallet.
- 7-zip - Supports strongly-encrypted archives.
- AxCrypt by Axantum
- lrzip - Compression software for Linux and OSX that supports very high grade password protected encryption
- TrueCrypt - Volume-based on-the-fly encryption (for advanced users)
There is also a list of open source encryption software.
Decrypting and encrypting the wallet.dat every time you start or quit the Bitcoin client can be tedious (and outright error-prone). If you want to keep your wallet encrypted (except while you're actually running the Bitcoin client), it's better to relegate the automation to a small shell script that handles the en/decryption and starting up Bitcoin client for you (Linux and OSX).
There is also a method to print out and encrypt your wallet.dat as a special, scannable code. See details here: WalletPaperbackup
Password Strength
Brute-force password cracking has come a long way. A password including capitals, numbers, and special characters with a length of 8 characters can be trivially solved now (using appropriate hardware). The recommended length is at least 12 characters long. You can also use a multi-word password and there are techniques to increase the strength of your passwords without sacrificing usability. The Usability of Passwords
However, simply using dictionary words is also insecure as it opens you up to a dictionary attack. If you use dictionary words, be sure to include random symbols and numbers in the mix as well.
If you use keyfiles in addition to a password, it is unlikely that your encrypted file can ever be cracked using brute-force methods, even when even a 12 character password might be too short.
Assume that any encrypted files you store online (eg. Gmail, Dropbox) will be stored somewhere forever and can never be erased.
Choosing A Strong Password
Make sure you pick at least one character in each group:
Lowercase: abcdefghijklmnopqrstuvwxyz
Uppercase: ABCDEFGHIJKLMNOPQRSTUVWXYZ
Number: 1234567890
Symbol: `~!@#$%^&*()-_=+\|[{]};:'",<.>/? (space)
<9 char = unsuitable for use 09 char = insecure 10 char = low security 11 char = medium security 12 char = good security (good enough for your wallet) 13 char = very good, enough for anything.
You might want to read What is your way to create good passwords that can actually be remembered? and XKCD #936: Short complex password, or long dictionary passphrase?
Email-based Archival and Remote Backup
One of the simplest methods for storing an appropriately encrypted archive of your wallet.dat file is to send the archive as an email attachment to your own e-mail address. Services like Gmail use very comprehensive distributed networks that make the loss of data very unlikely. One can even obfuscate the name of the files within the archive, and name the archive something less inviting, such as: 'personal notes' or 'car insurance'.
Another solution is to use a file storage service like Wuala ( encrypted, instructions), Dropbox (after encrypting the wallet first) and others, including the more secure SpiderOak.
Automated Backups using Cron, Bash and GNU/Linux
Linux users can setup backups using cron by telling it to run a backup script at set intervals of time. Run 'crontab -e' and add this line near the bottom:
01 * * * * /usr/local/bin/backupwallet.sh
This cron line will run the /usr/local/bin/backupwallet.sh script at the 01 minute of every hour. Remember to add a newline after the last line of the crontab file, or else the last line won't run. You may also wish to ignore the script's output by appending " > /dev/null 2>&1" to the line (this will also prevent emails from being sent).
Create /usr/local/bin/backupwallet.sh:
#!/bin/bash # /usr/local/bin/backupwallet.sh # # Performs backup of bitcoin wallet. # # Written by: https://en.bitcoin.it/wiki/Securing_your_wallet # # Standard Options # TS=$(date "+%Y%m%d-%H%M") WALLET=/tmp/wallet-${TS} WALLET_E=/tmp/wallet-${TS}.crypt BITCOIN=bitcoind # /path/to/bitcoind GPG=gpg # /path/to/gpg GPG_USER=username # Username of gpg recipient. User should have gpg setup. RM=rm RM_OPTS='--force' USE_SHRED=0 # Flip to 1 to use `shred` instead of `rm`. SHRED=shred SHRED_OPTS='--force --iterations=9 --zero --remove' # # Storage Options # Only 1 set of options should be un-commented (the last one will be used). # Update CP_DEST paths as neccessary. # # CP - Storage on a local machine. Could be Dropbox/Wuala folder. #CP=cp #CP_DEST='/var/data/backups/' # '~/Dropbox/', etc. # # SSH - Storage on a remote machine. CP=scp CP_DEST='remoteuser@example.com:~/wallets/' # # S3 - Storage on Amazon's S3. Be sure s3cmd is installed and properly setup. # You may need "s3cmd put --force" if you use a sub-directory in CP_DEST. #CP=s3cmd put #CP_DEST='s3://bucket' do_clean() { # Remove temporary wallets. if [ 1 -eq $USE_SHRED ]; then $SHRED $SHRED_OPTS $WALLET $WALLET_E else $RM $RM_OPTS $WALLET $WALLET_E fi } do_fail() { do_clean echo failed! exit 1 } # Perform the backup. echo -n Making backup... $BITCOIN backupwallet $WALLET [ ! -s "$WALLET" ] && do_fail # If the backup does not exist or is empty, fail. echo done. echo -n Encrypting backup... $GPG -r $GPG_USER --output $WALLET_E --encrypt $WALLET [ 0 -ne $? ] && do_fail # If gpg returns a non-zero result, fail. echo done. echo -n Copying to backup location... $CP $WALLET_E "$CP_DEST" [ 0 -ne $? ] && do_fail # If the $CP command returns a non-zero result, fail. echo done. do_clean exit 0
The shell script:
- Calls bitcoind backupwallet to create a time/date-stamped wallet.
- GPG encrypts the wallet with your public key.
- Copies the result using one of several storage options (cp, scp, and s3cmd).
- Uses the rm or shred command to remove the temporary wallet files.
Be sure to modify the script options to fit your setup. After you save, make sure the file can be executed properly by the cron user. Common permissions for files in /usr/local/bin/ can be applied using (verify with your distribution!):
cd /usr/local/bin/ && chown root:root backupwallet.sh && chmod 755 backupwallet.sh
Restore
Assuming your backup is recent enough that you haven't used up all of your key pool... restoring a wallet to a new (or old) location and rescanning the block chain should leave you with all your coins. Just follow these steps:
- Shut down the Bitcoin program.
- Copy your backed-up wallet.dat into your bitcoin data directory.
- If you are copying in a backed-up wallet.dat that was last used on a Bitcoin version prior to 0.3.21 into an existing profile, delete files blk*.dat to make the client re-download the block chain. You may also need to do this if your transactions don't all show up after you restart Bitcoin.
Erasing Plain-text Wallets
In most operating systems, including Windows, Linux, and Mac OS X, simply deleting a wallet.dat file will not generally destroy it. It is likely that advanced tools can still be used to recover the wallet.dat file, even after it has been deleted.
The Linux shred command can be used to overwrite the wallet file with random data prior to deleting; this particular copy of the file will then be practically impossible to recover. Using shred (and similar tools on Windows) however does not guarantee that still other copies don't exist somewhere hidden on your HD. That will depend on your system configuration and what packages you have installed. Some system restore and backup tools, for instance, create periodic snapshots of your filesystem, duplicating your wallet.dat.
In Mac OS, the equivalent of shred is srm (introduced in Leopard). Using the Finder to remove files, clicking "Secure Empty Trash" in the Finder menu will shred the contents of the trash can. As with any OS this doesn't guarantee that there are not other copies elsewhere on your system.
For Windows, the built-in command cipher /W will shred all previously-deleted files. CyberShredder can securely deleted individual files.
Online and Mobile Wallets
Thus far, this article has been discussing the security of a wallet file for Bitcoin-QT or bitcoind that is under your sole control. Additional wallets applications and services have become available that offer other features and more convenience but not without introducing additional risk. When storing bitcoins with an eWallet such as Instawallet or Easywallet, you are essentially storing your private keys or wallet with that provider.
Online wallets have a number of pros and cons to consider. For example, you can access your wallet on any computer in the world, but depending on the service, your bitcoins may be lost if the service is compromised.
Mobile wallet applications are available for Android devices that allow you to send bitcoins by QR code or NFC, but this opens up the possibility of loss if mobile device is compromised. It may be possible to encrypt and backup the wallet or private keys on a mobile device but it is not advisable to store a large amount of bitcoins there without doing your own research and testing.